AI HIPAA Compliance Monitoring Agent
Automating HIPAA Compliance Monitoring with AI
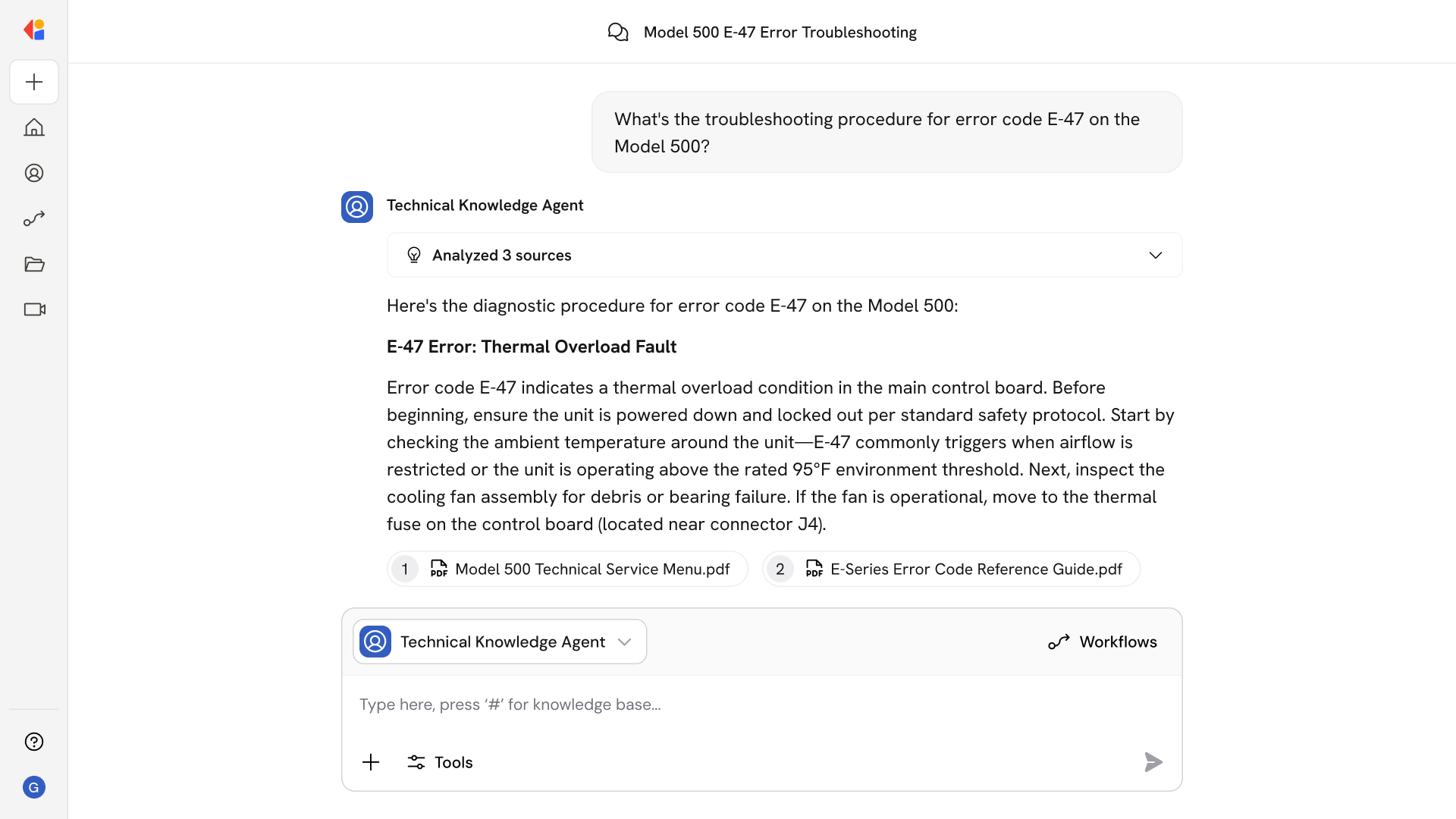
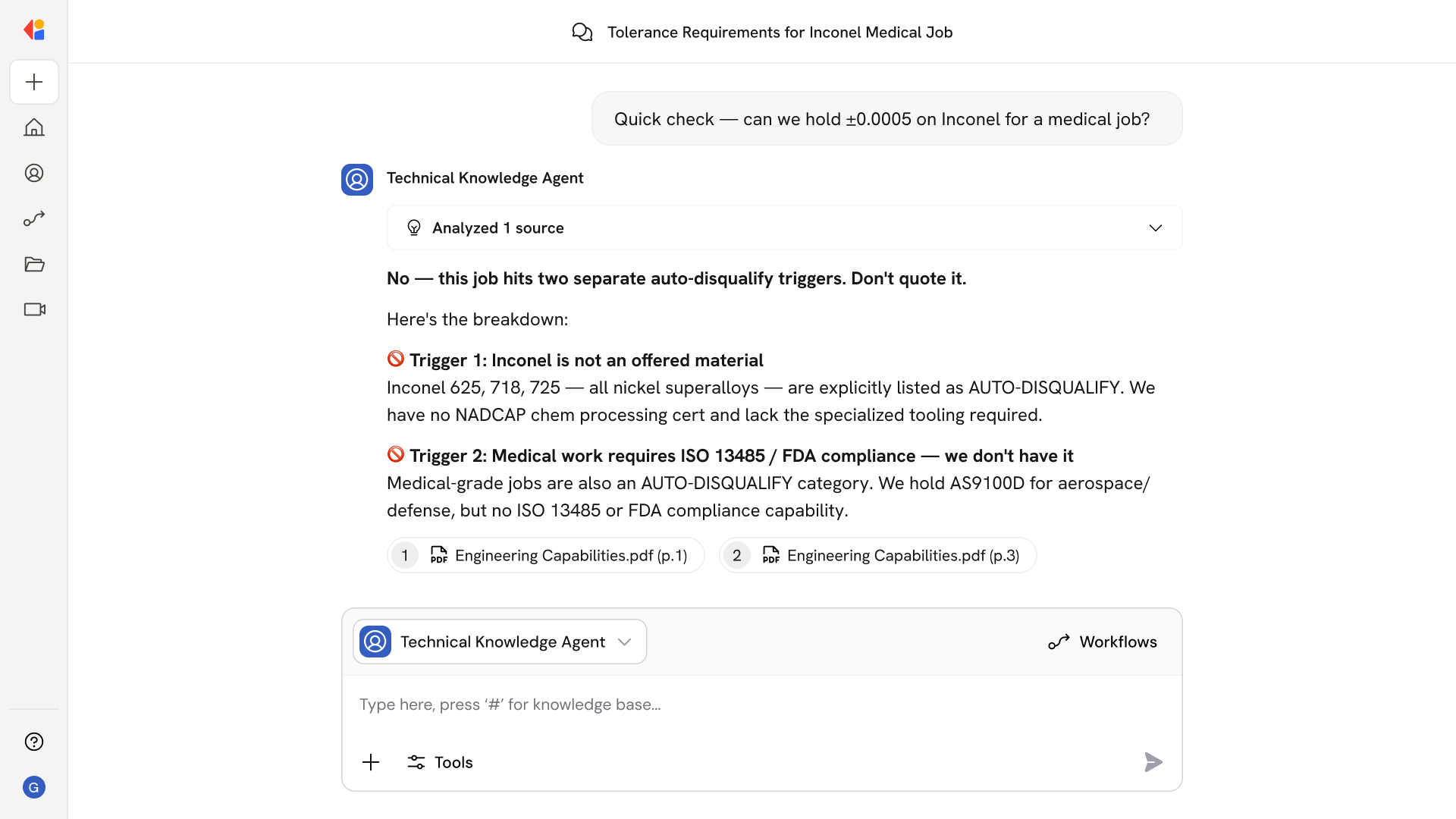
Continuous ePHI Access Surveillance
AI automation monitors EHR access logs, authentication events, and data movement in real time, baselining normal user behavior and flagging deviations that could indicate snooping, unauthorized access, or potential breaches.
Risk-Scored Alert Triage and Investigation
The system combines UEBA anomaly scores with contextual factors—care relationships, break-the-glass justifications, and role mappings—to prioritize alerts, auto-generate evidence packs, and route cases to Privacy Officers with full audit trails.
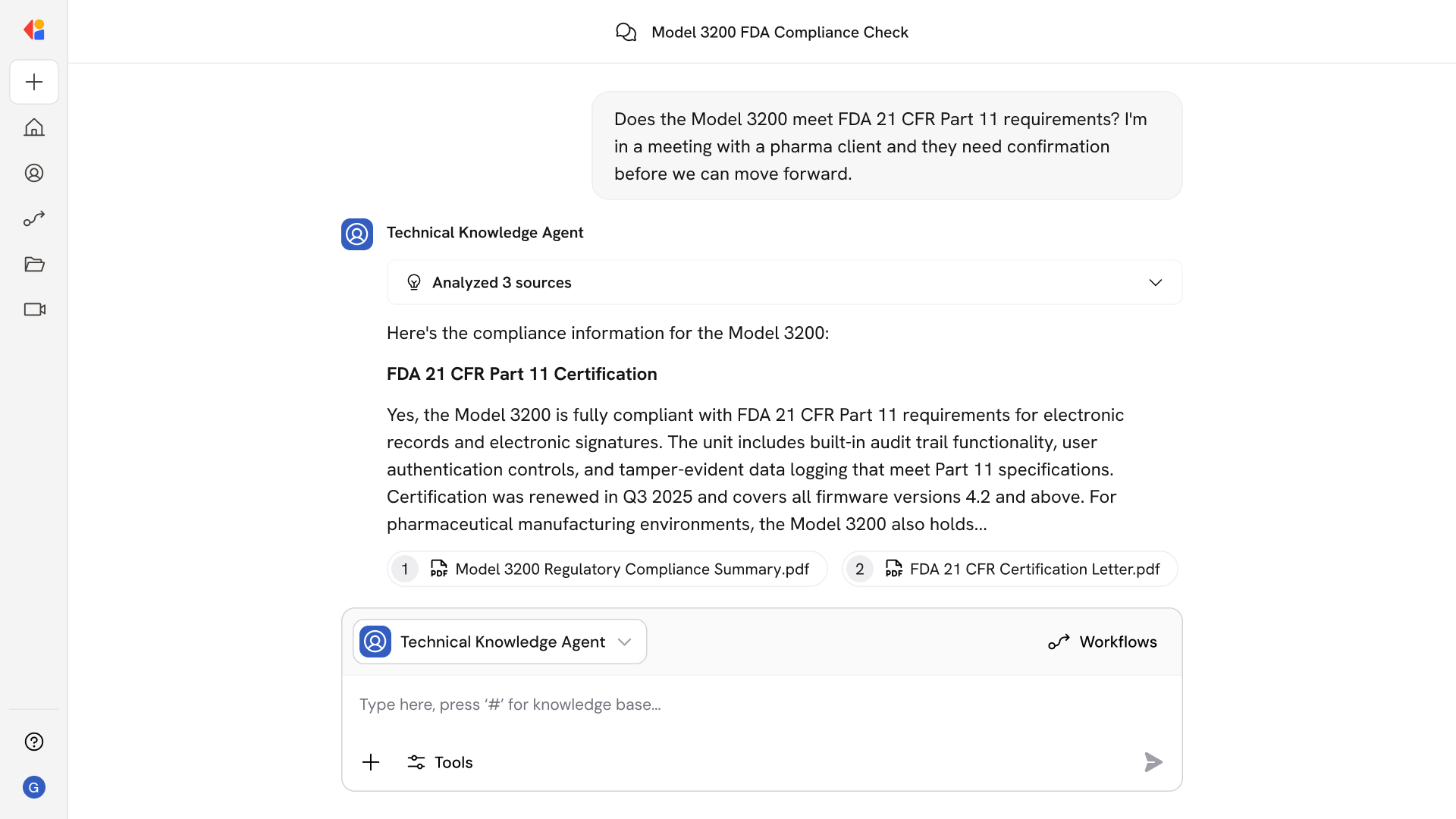
Audit-Ready Documentation on Demand
Automated workflows produce OCR-aligned reports mapped to Security Rule citations, including information system activity reviews, access control samples, breach risk assessments, and corrective action tracking—ready for regulatory scrutiny.
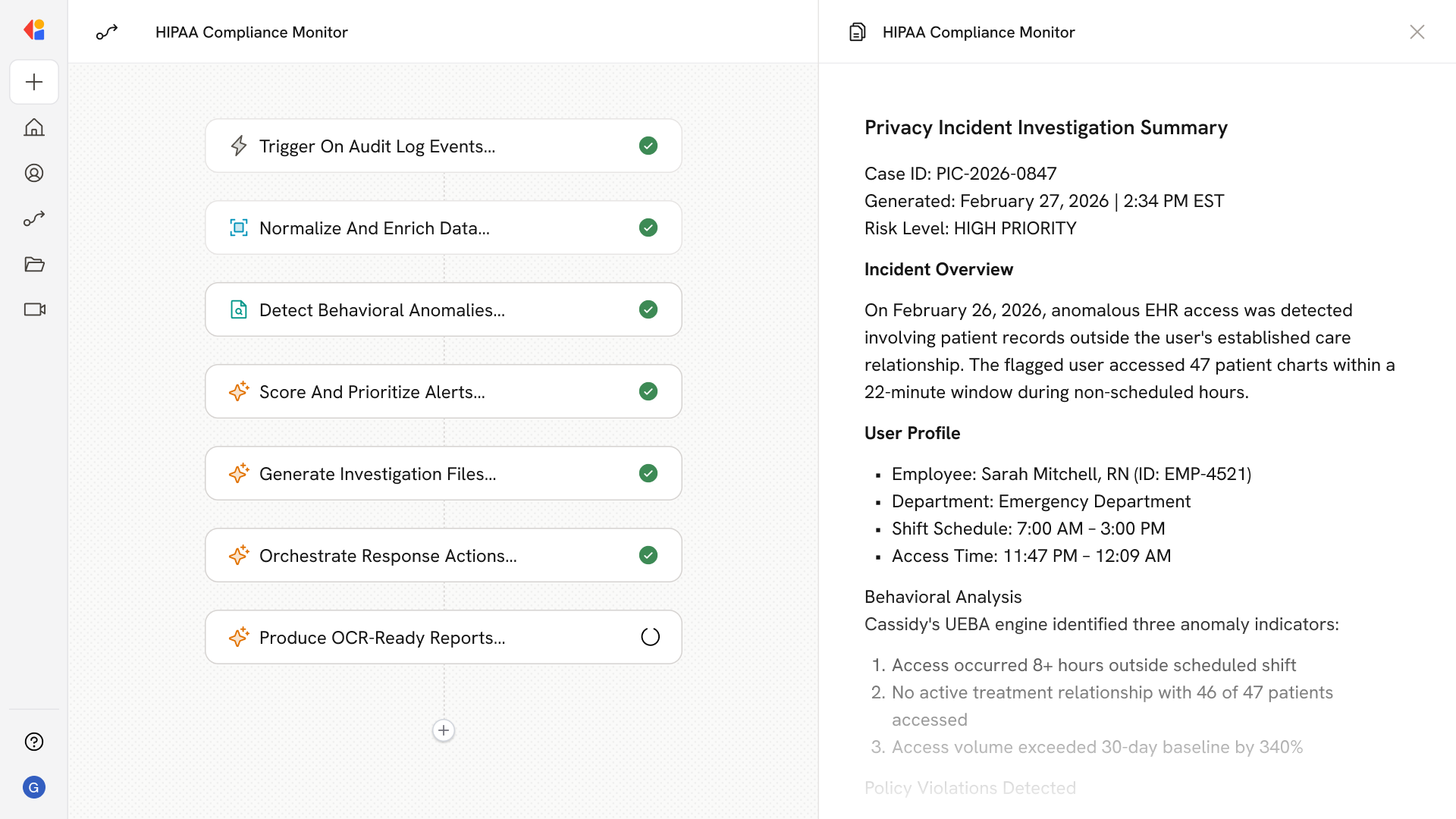
How Cassidy automates this using AI
Step 1: Trigger on audit log events
The Workflow activates when new EHR access logs, authentication events, or DLP alerts arrive—whether via API, syslog, or FHIR event streams from your ePHI systems.
Step 2: Normalize and enrich event data
Cassidy standardizes log formats across EHRs and ancillary systems, then enriches each event with identity context from IAM/SSO, HR roster data, care relationship lookups, and shift schedules to establish baseline expectations.
Step 3: Apply UEBA and policy-based detection
The Workflow runs behavioral analytics to detect anomalies—VIP chart access, off-hours activity, bulk record pulls, or access outside treatment relationships—while layering deterministic rules for known privacy risks like coworker snooping or excessive privileges.
Step 4: Risk-score and prioritize alerts
Cassidy calculates a composite risk score combining anomaly severity, policy violations, and contextual factors, then routes high-priority cases to your Privacy Officer queue with lower-risk events batched for periodic review.
Step 5: Auto-generate investigation case files
For flagged events, Cassidy assembles evidence exhibits: event timelines, user profiles, care relationship verification, policy rationale, and hashed log excerpts—ready for investigator review without manual assembly.
Step 6: Orchestrate response and sanctions workflows
The Workflow notifies relevant stakeholders, collects user attestations, and integrates with HR systems to document corrective actions and sanctions per your progressive discipline policy.
Step 7: Produce OCR-ready compliance reports
Cassidy generates audit-ready documentation mapped to OCR Audit Protocol controls—including information system activity reviews, access management samples, incident response records, and breach risk assessments with chain-of-custody attestations.
Implement it inside your company
- Hands-on onboarding and support
- Self-paced training for your team
- Dedicated implementation experts
- Ongoing use case discovery
- ROI tracking & analytics dashboards
- Proven playbooks to get started fast